Solutions & Technologies
Data Center Networks
Scale innovation and embrace the AI revolution — reliably, simply, securely
Whether supporting traditional application and storage interconnection demands or managing the unique requirements for connecting AI workloads, businesses require fast and reliable on-premises data center networks that perform like the cloud. However, as data center network operations become increasingly complex, skilled IT resources continue to be in short supply. Juniper’s Data Center solutions are the fastest and most flexible way to deploy high performing networks, and the simplest to operate with limited IT.
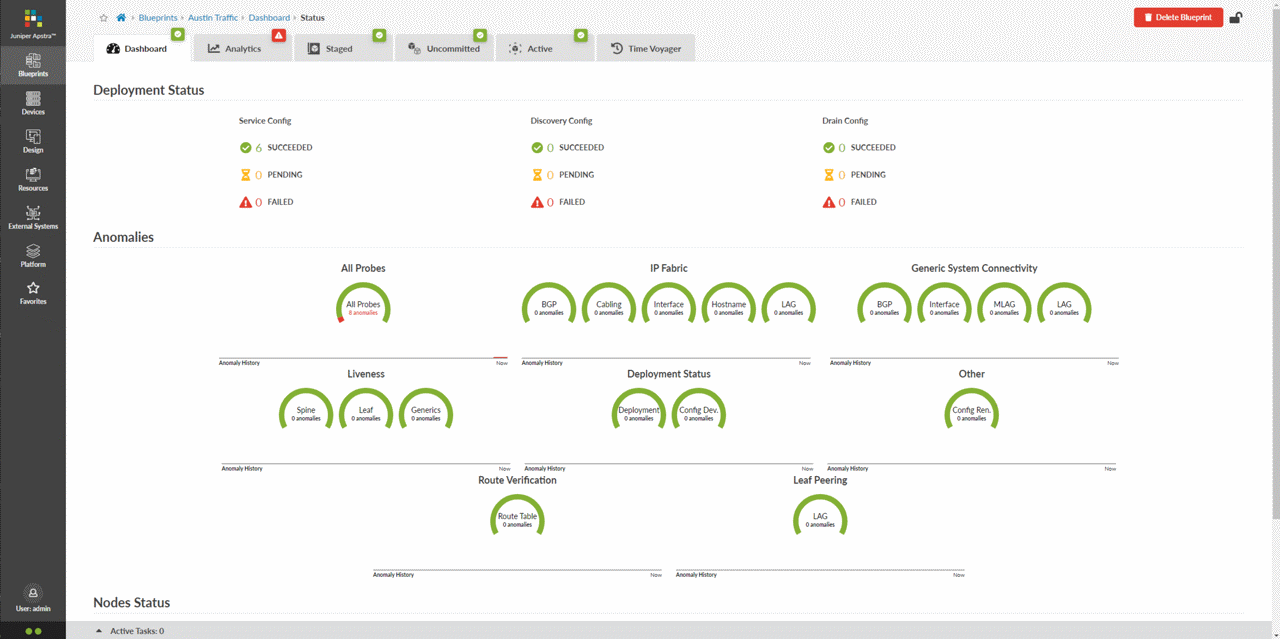
Juniper Apstra delivers reliable intent-based automation and operational excellence throughout the entire Day 0 to Day 2+ lifecycle over a wide range of topologies and switches without vendor lock-in. And the Apstra integration of our Marvis virtual network assistant (VNA) brings AIOps to the data center, further elevating operator and end-user experiences.
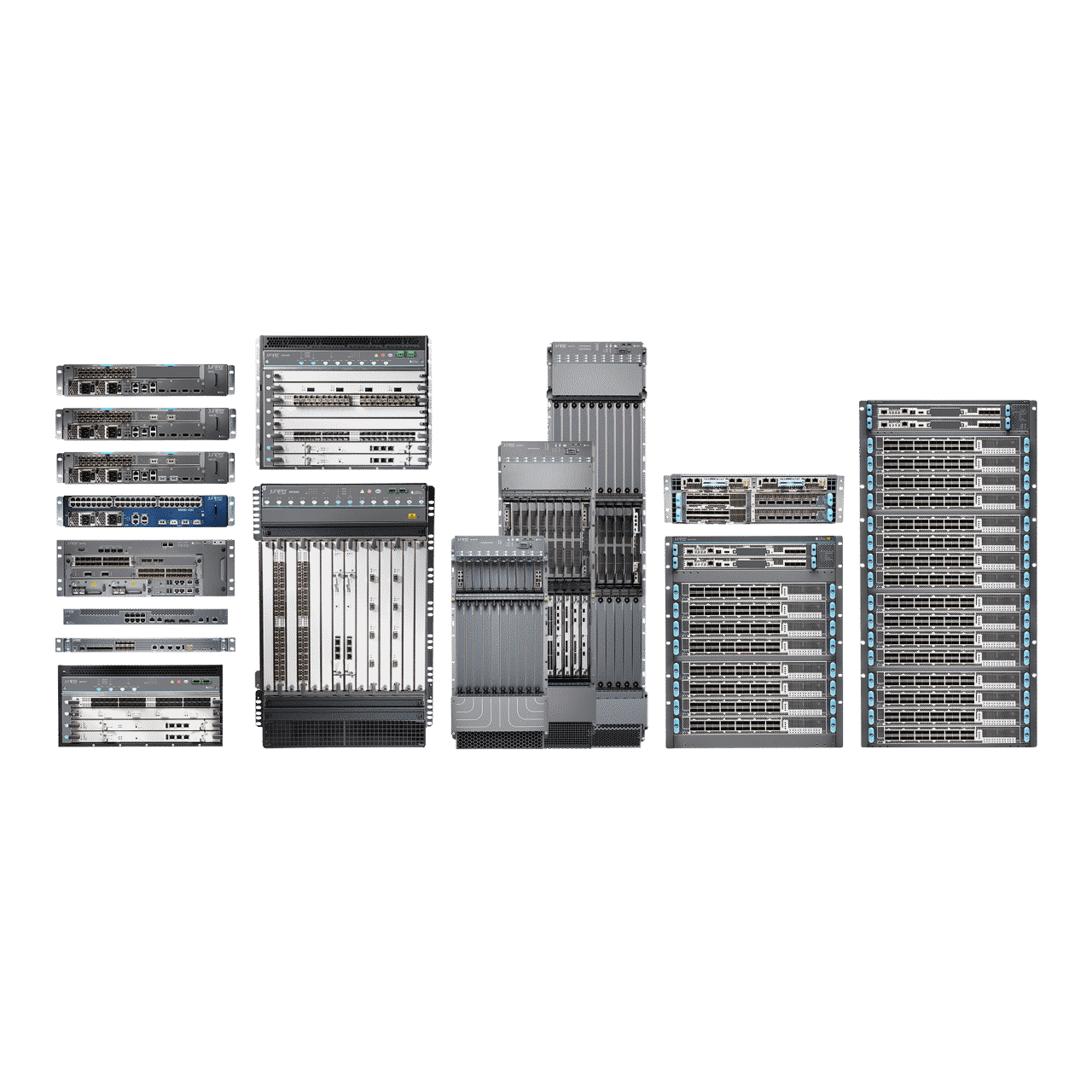
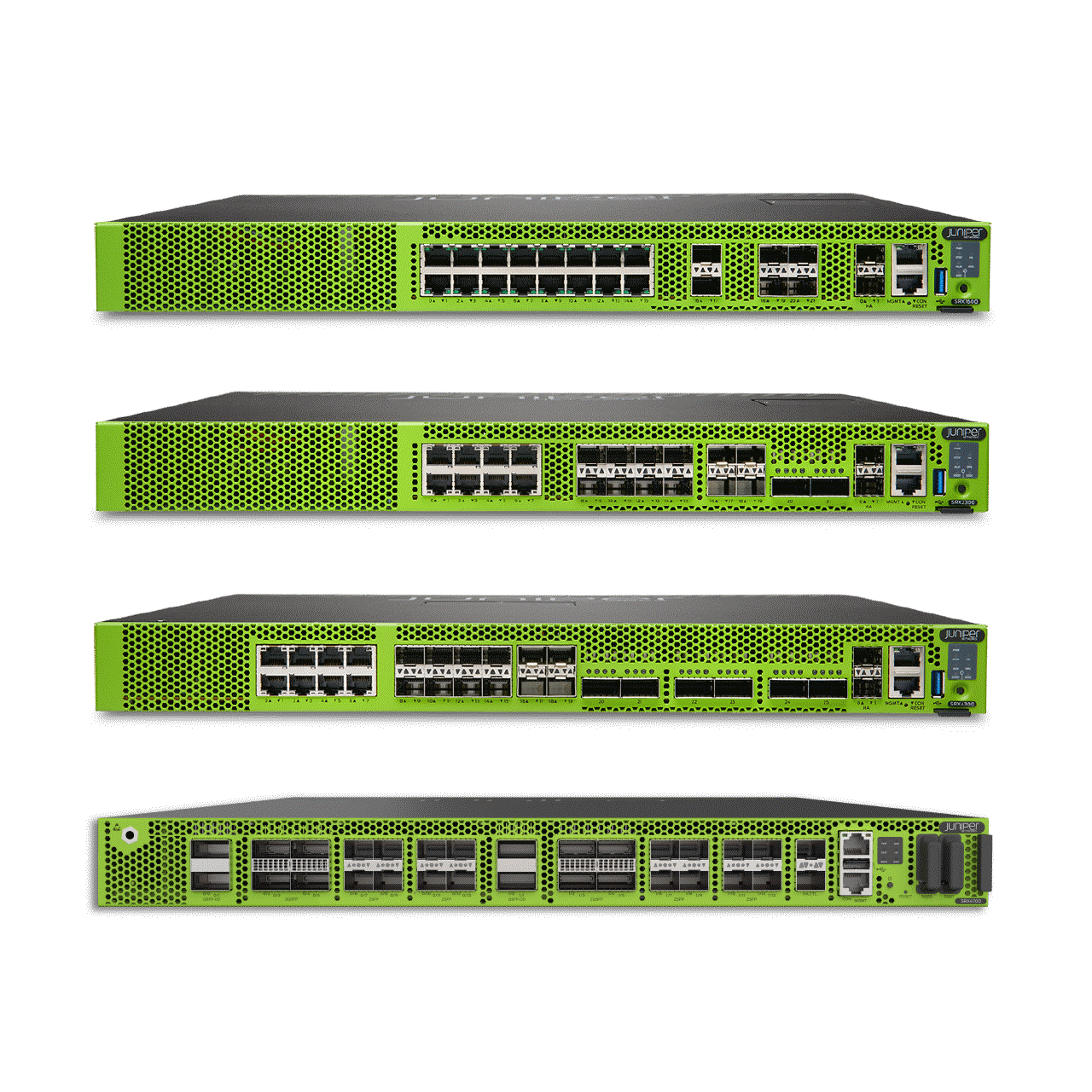
Juniper’s switching, routing, and security platforms deliver a scalable data center foundation with resilient, automated fabrics and built-in threat prevention. And our comprehensive security portfolio ensures zero-trust data center architectures that safeguard users, applications, data, and infrastructure across all network connection points.

Ease the pain of data center migration
How Juniper can help
Success in today’s fast-paced business environment demands agility, reliability, and speed. Juniper helps you modernize and automate your data center infrastructure and operations to achieve all three.

Simplified operations save time and money
Juniper Apstra automates and validates the design, deployment, and operations of your data center network, resulting in 90% lower OPEX and 85% faster deployment. Simply define the outcomes you need — Apstra responds by setting up the network, automating network management to ensure it’s secure and runs as intended. And with Marvis VNA for the Data Center, you gain a single Marvis dashboard for proactive and prescriptive data center actions. In addition, knowledgebase queries are simplified using the Marvis conversational interface (powered by GenAI).

Open flexibility drives innovation and avoids lock-in
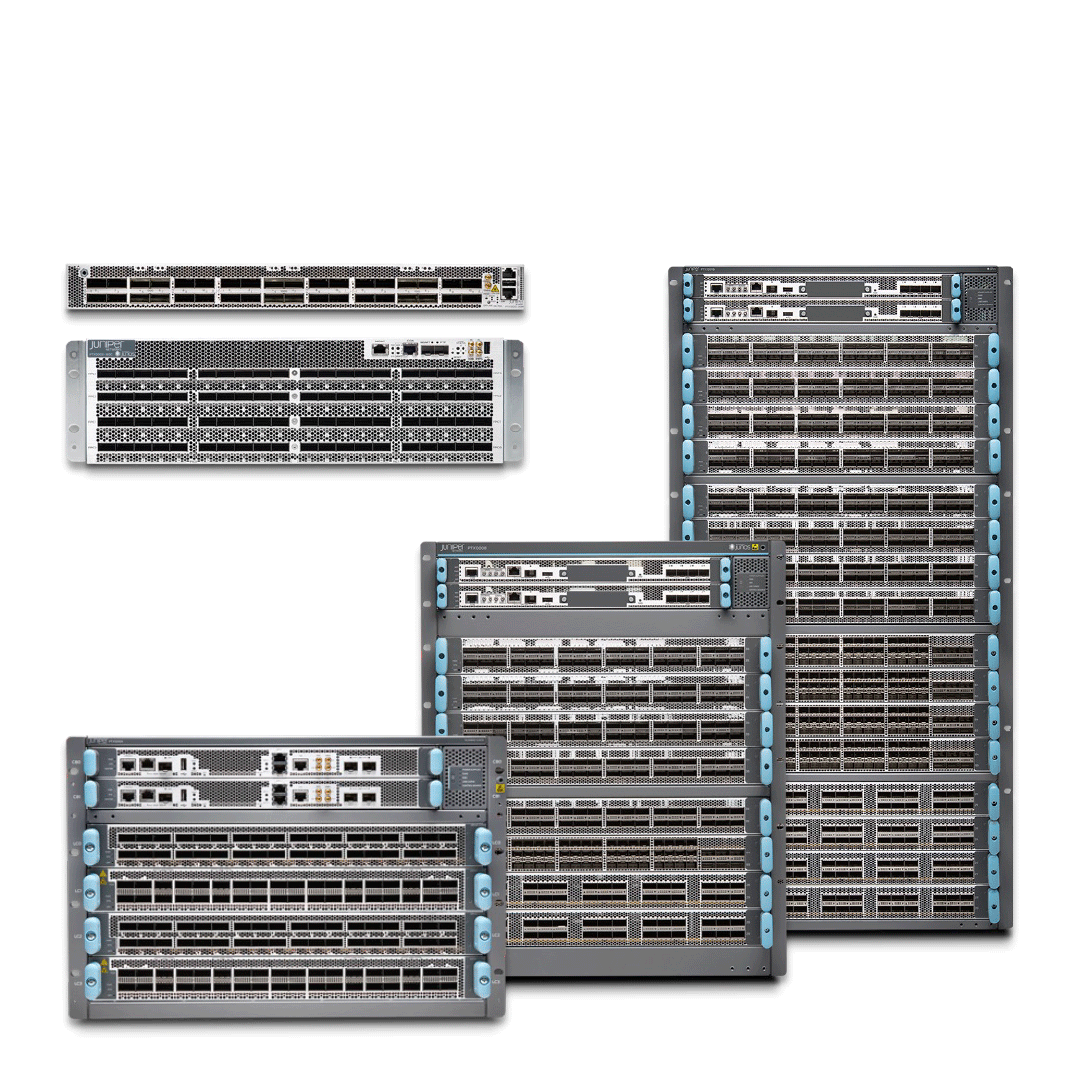
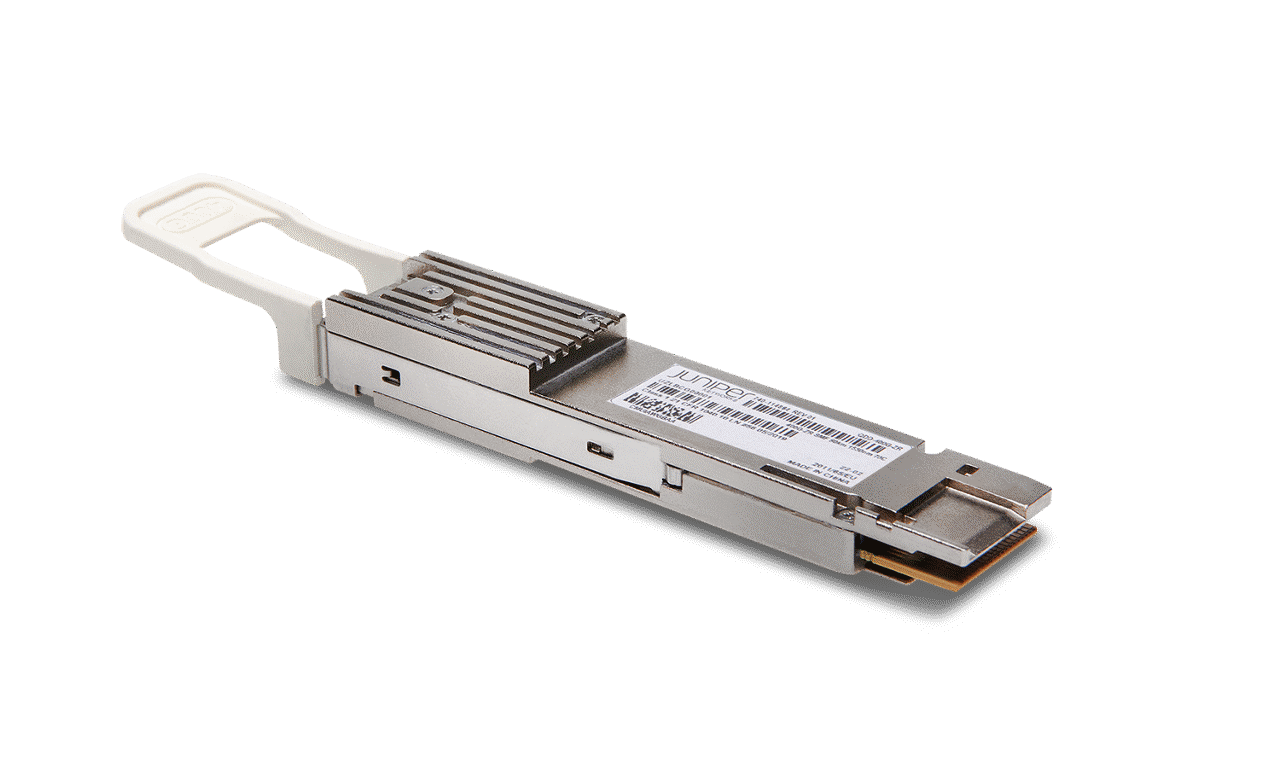
Juniper's new AI-optimized, high-radix 800GbE leaf and spine data center fabrics provide advanced traffic management capabilities, ensuring high bandwidth, low latency, lossless, and scalable performance over Ethernet. Just as important, they reduce costs, accelerate innovation, maximize design flexibility, and help you avoid vendor lock-in. Our standards-based, automated network fabrics deliver scalability, reliability, and nonblocking, predictable performance. QFX Series, PTX Series, and ACX Series switches and routers offer leading throughput and scale with 400G interfaces, the Junos operating system’s open programmability, and comprehensive EVPN-VXLAN and IP fabric capabilities.

Validated solutions with unified zero-trust security
Juniper Validated Designs (JDVs) assure a complete data center solution, from switching and routing to operations and security. Our broad portfolio of switches (with silicon diversity) drive scale and performance, and a comprehensive DC security portfolio with unified threat prevention delivers unified zero-trust data center protection to safeguard users, applications, data, and infrastructure across all network connection points. With trusted, turnkey data center solutions from Juniper, you can confidently deploy new services 10x faster.
CUSTOMER SUCCESS
AI-driven, zero trust network yields business agility for AmeriTrust
AmeriTrust, a specialty insurance commercial underwriter and administration services company, looked to digital transformation to fuel growth. It embarked on an ambitious effort to streamline IT operations, strengthen cybersecurity, and drive business success in an unpredictable and changing world.

Resource Center
Demos
Technical Documentation
Analyst Reports
Whitepapers
Solution Briefs
Videos
Webinars
Blogs
Infographics
Press Releases
Articles
Related Solutions
AI Data Center
Deploy high performing AI training, inference, and storage clusters with speed and flexibility.
Data Center Interconnect
Juniper’s DCI solutions enable seamless interconnectivity that breaks through traditional scalability limitations, vendor lock-in, and interoperability challenges.
400G & 800G
Juniper offers the industry’s most comprehensive and high-performing 400G and 800G routing and switching platforms: PTX Series Packet Transport Routers, MX Series Universal Routing Platforms, ACX Series Routers, and QFX Series Switches. These platforms increase efficiencies throughout your infrastructure while keeping your network secure and highly customizable.
Automated Secure Data Center
The Juniper automated secure data center unites the multivendor automation and assured reliability of intent-based networking software with Juniper’s scalable and programmable switching and routing platforms.
IP Storage Networking
Simplify your data storage and boost data center performance with all-IP storage networks. Use the latest technologies, such as NVMe/RoCEv2 with 100G/400G switching or NVMe/TCP, to build high-performance storage or converge your storage and data into a single network.
Converged Optical Routing Architecture (CORA)
CORA is an extensible, sustainable, automated solution for IP-optical convergence. It delivers the essential building blocks operators need to deploy IP-over-DWDM transformative strategies for 400G networking and beyond in metro, edge, and core networks.
Zero Trust Data Center Security
Juniper Zero Trust Data Center Security protects your distributed centers of data by operationalizing security and extending zero trust across networks to prevent threats with proven efficacy. With unified management, context-driven network-wide visibility, and a single policy framework, Juniper safeguards users, data, and infrastructure across hybrid environments.
Cloud-Native
Juniper cloud-native solutions go far beyond basic connectivity by delivering the scale, performance, and security levels that can free your DevOps team from unneeded complexity and let them focus instead on application innovation.
Bringing AI to Enterprise Networking
Demand more from your network
Data Center Networks FAQs
What is the Juniper Data Center Networks solution?
The Juniper Data Center Networks solution is a combination of intent-based networking automation software, AIOps, best-in-class routers and switches, and a distributed security services fabric. It helps you build crash-resistant networks and boosts reliability in networks of all sizes while enabling zero-trust access control and policy enforcement across all network connections.
What components make up the Juniper Data Center Networks solution?
The solution comprises a wide range of products, including:
- Juniper Apstra software for intent-based, highly reliable network automation and lifecycle management
- Marvis VNA for data center, which brings additional insight via proactive actions and a conversation interface for seamless knowledgebase queries.
- QFX, PTX, and ACX Series switching and routing platforms for best-in-class throughput and scale
- Juniper Connected Security distributed services fabric for creating a zero-trust data center network
What data center networking challenges does the solution address?
The Juniper solution addresses the biggest, most universal networking challenges that IT faces:
- Traditional CLI and DIY automation for data center management is difficult to scale and prone to network failures.
- As networks scale up, they become difficult to monitor, requiring real-time data analytics to ensure continuous validation.
- There are shortages of skilled staff, and specialists must know the tools and CLI of several vendors.
- Dated hardware is complicated to manage and not well-suited for scaling.
- Internal and external security incidents can cause expensive outages.
How does the Juniper Data Center Network solution address today’s data center challenges?
The solution addresses the challenges described above in the following ways:
- Unreliable Automation – Juniper Apstra intent-based networking software automates and validates the design, deployment, and operation of data center networks, from Day 0 through Day 2+.
- Monitoring at scale/analytics – Using a single source of truth, powerful analytics, and root-cause identification, Apstra quickly pinpoints and resolves issues. It allows network operators to customize telemetry collection and explore and visualize the data with an easy-to-use, no-code Graph Explorer.
- Skillset shortages – Juniper Apstra is the only multivendor data center automation software of its kind. It does away with a CLI and hence the need for vendor-specific skills, so you can hire flexibly without vendor certification limitations.
- Hardware management and scalability – QFX Series Switches deliver industry-leading throughput and scalability, the open programmability of the Junos OS, and a broad set of EVPN-VXLAN and IP fabric capabilities. Combined with the management prowess of Apstra, they’re an optimal choice in enterprise, service provider, and cloud provider environments.
- Security threats – The data center solution works with the Juniper Connected Security distributed services fabric of physical, virtual, and containerized SRX Series Firewalls to deliver a zero-trust experience. Protection extends across users, applications, and data wherever they are, in the data center, network edge, or the cloud.
What are the deployment options for Juniper Data Center Networks?
A number of training and professional services are available to meet your needs, including recommendations on best products and live demos. To learn more, connect with your Juniper sales representative or contact us.
How can Juniper help modernize data center infrastructure?
The Juniper Data Center Networks solution comprises power-efficient and expansion-friendly switches, next-generation firewalls, and intent-based fabric management that scale up reliably and optimize automation to ease network management.
Who should consider using the Juniper Data Center Networks solution?
All organizations looking to build, scale, or modernize their data centers should consider using the solution. We offer you the flexibility to grow and gain new management and cost efficiencies, all without sacrificing reliability.